OAuth 2.0 Client Credentials Flow for Machine-to-Machine Communication
The diagram illustrates the OAuth 2.0 Client Credentials Flow between the ACS (third-party software) and the ACS (other third-party software) using the HIN Identity Provider (IDP).
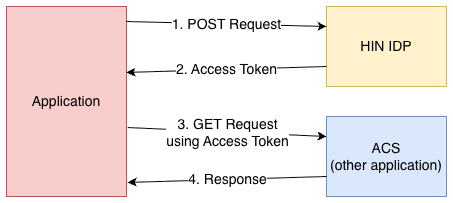
Step-by-Step Explanation:
- POST Request with Client Credentials to HIN (IDP): The application sends a POST request with its client credentials to HIN (IDP) to obtain an access token.
Note: In the Client Credentials Flow, the requirement for an authorization code is omitted. - Access Token from HIN (IDP): HIN (IDP) validates the client credentials and responds with an access token, which is sent to the application.
- Access to Protected Resources with Access Token: The application uses the access token to send a GET request to the ACS (other application) and access the protected resources.
- Data Transfer between ACS (other third-party software) and ACS (other application): The ACS (other application) validates the access token and enables access to the requested data, which is then transferred to the application.